An advanced captcha plugin should do more than show a challenge: it should fit your stack, validate reliably on the server, support your users’ languages and devices, and keep bot traffic from turning into a support problem. If a plugin can’t do those things cleanly, it’s not advanced—it’s just another widget.
That sounds simple, but the details matter. A good implementation lives across the client and server boundary, gives you a predictable token flow, and avoids turning your login, signup, checkout, or form pages into a usability tax. If you’re evaluating options like reCAPTCHA, hCaptcha, Cloudflare Turnstile, or a newer provider such as CaptchaLa, the right question is less “Which one is famous?” and more “Which one fits my application and my risk profile?”
What “advanced” actually means in a captcha plugin
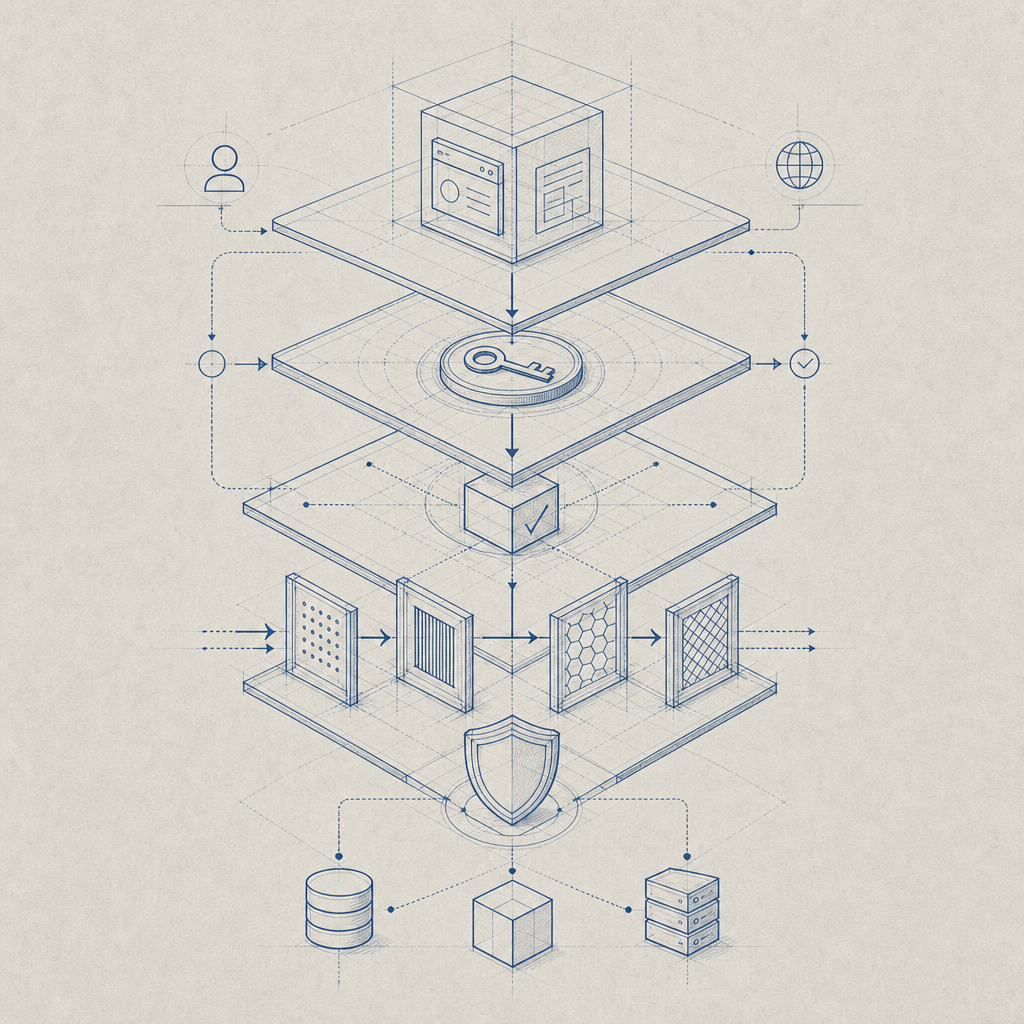
A lot of products call themselves advanced because they include invisible checks, risk scoring, or adaptive challenges. Those features can be useful, but they are only one part of the picture. From a defender’s perspective, “advanced” usually means the plugin handles four jobs well:
It integrates cleanly across platforms.
Web apps are only part of the story. Mobile apps, desktop wrappers, and hybrid stacks often need protection too. A mature plugin should offer native support where it matters.It produces a verifiable server-side token flow.
Client-side widgets are easy to fake if the backend accepts them at face value. The plugin should generate a pass token that your server validates directly.It doesn’t create unnecessary friction.
Good bot defense minimizes user annoyance. It should be able to challenge suspicious behavior without punishing everyone else.It gives you operational control.
You need logs, clear API behavior, and a setup that your team can actually maintain after launch week.
CaptchaLa is a good example of a plugin ecosystem that focuses on those fundamentals: 8 UI languages, native SDKs for Web (JS, Vue, React), iOS, Android, Flutter, and Electron, plus server SDKs for PHP and Go. That breadth matters because the “advanced” part is often not the widget itself, but how well it fits into your app architecture.
A practical checklist for evaluation
If you’re comparing an advanced captcha plugin, use a checklist like this instead of relying on marketing claims.
1) Does it support your real stack?
Look beyond plain HTML forms. Ask whether the plugin works with:
- SPA frameworks such as React and Vue
- Native mobile apps
- Cross-platform apps like Flutter
- Desktop shells such as Electron
- Server-side rendering and API-first flows
If your product spans multiple surfaces, a single integration style can become a maintenance headache. In that case, native SDK coverage is a real advantage.
2) How does validation work?
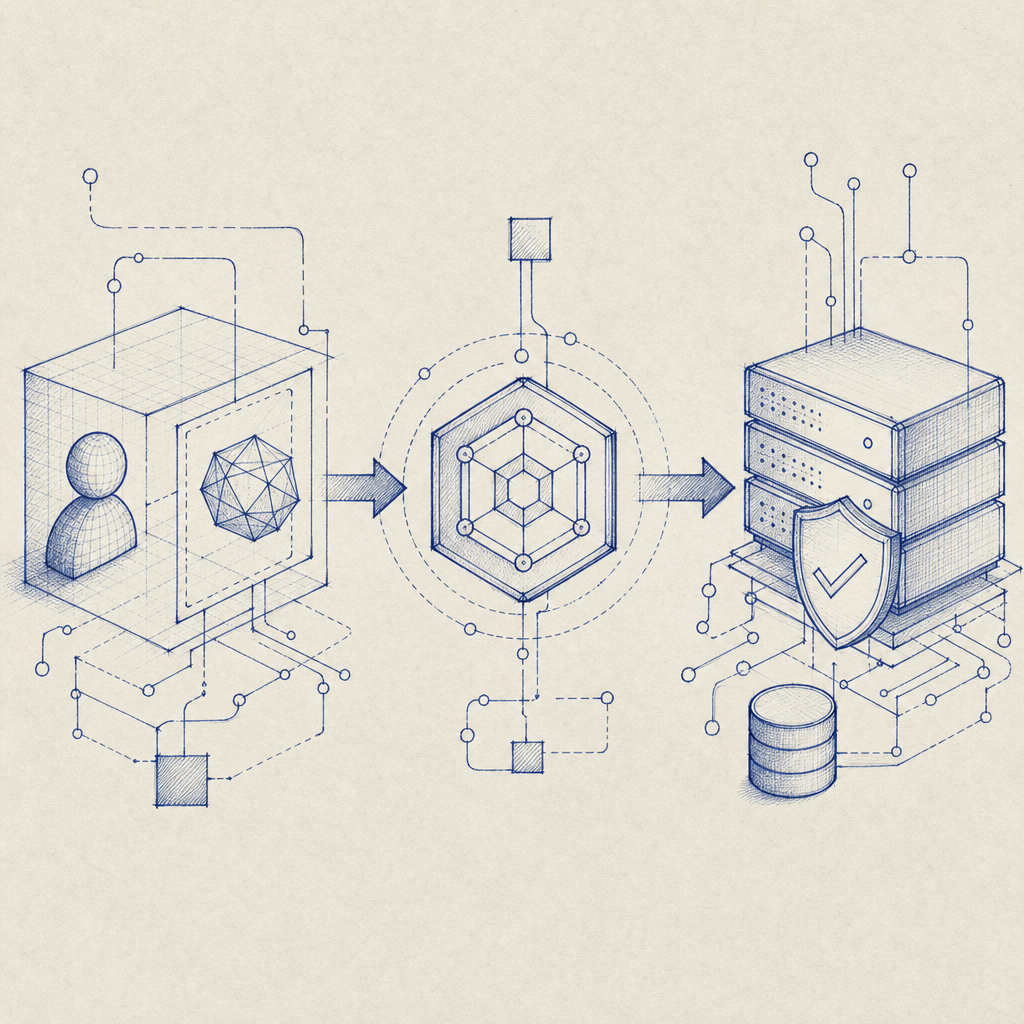
The most important part of any captcha is the server validation step. A strong implementation usually looks like this:
- the client completes a challenge
- the client receives a pass token
- the server validates that token with the provider
- your app decides whether to allow the action
For CaptchaLa, server validation happens with a POST request to:
https://apiv1.captcha.la/v1/validate
The request body includes pass_token and client_ip, and you authenticate with X-App-Key and X-App-Secret. That pattern is useful because it keeps trust decisions on your backend, where they belong.
3) Is there a clear server-token flow?
Some apps need a challenge issued from the backend before the user ever sees anything. For those cases, a server-token endpoint can help you coordinate challenge issuance more precisely. CaptchaLa provides a server-token endpoint at:
POST https://apiv1.captcha.la/v1/server/challenge/issue
That can be especially useful when you want to gate sensitive actions, throttle suspicious sessions, or tie a challenge to a specific transaction.
4) Does it fit your deployment constraints?
You may care about package ecosystems as much as features. Here are a few concrete examples:
- Java:
la.captcha:captchala:1.0.2 - iOS:
Captchala 1.0.2via CocoaPods - Flutter:
captchala 1.3.2on pub.dev - PHP server SDK:
captchala-php - Go server SDK:
captchala-go
That kind of coverage reduces custom glue code, which is often where integration bugs creep in.
Comparison snapshot
| Product | Common strengths | Things to verify |
|---|---|---|
| reCAPTCHA | Familiar to many teams, broad ecosystem | User experience, data handling, and implementation fit |
| hCaptcha | Strong anti-bot focus, flexible deployment | Challenge friction and integration details |
| Cloudflare Turnstile | Low-friction approach, simple web integration | Coverage outside Cloudflare-centric setups |
| CaptchaLa | Multi-platform SDKs, server validation APIs, first-party data only | Match against your exact app and traffic patterns |
This isn’t a ranking; it’s a reminder to compare based on your stack, UX tolerance, and operational needs.
Implementation details that separate good from great
An advanced captcha plugin is rarely judged by one feature. It’s judged by how well the pieces work together under load, in production, and across edge cases.
Keep the client simple
Your frontend should do as little as possible beyond rendering the challenge and collecting the pass token. A cleaner client reduces bugs and makes it easier to swap frameworks or update UI components later.
For example, a web integration might look conceptually like this:
// Load the captcha client library
const script = document.createElement('script');
script.src = 'https://cdn.captcha-cdn.net/captchala-loader.js';
script.async = true;
document.head.appendChild(script);
// After challenge completion, send token to your backend
async function submitWithCaptcha(passToken) {
const response = await fetch('/api/validate-action', {
method: 'POST',
headers: { 'Content-Type': 'application/json' },
body: JSON.stringify({
pass_token: passToken
})
});
return response.json();
}The exact wiring depends on your framework, but the pattern is the same: let the client collect proof, and let the server decide.
Put policy on the backend
Once the server validates a token, your application can apply policy based on the action and risk level. For instance:
- allow the request immediately
- require additional verification
- rate-limit the session
- log the event for review
- deny the action and return a generic error
That backend-first approach is especially important for login, registration, password reset, account recovery, and checkout flows.
Respect users without making security weaker
Modern bot defense should aim for minimal interruption. Users often notice captchas only when they are broken or too frequent. If your plugin supports adaptive challenge behavior, session-aware logic, or selective enforcement, you can protect sensitive paths without making every visit feel suspicious.
CaptchaLa’s 8 UI languages also help when your audience is not monolingual. That may sound like a small detail, but language coverage is often the difference between a confusing prompt and a straightforward interaction.
Deployment and operations: what your team will care about later
The first integration is only half the story. A plugin becomes “advanced” when it stays manageable after launch.
Questions to ask before production
Can we rotate keys without downtime?
Any system using app key and secret pairs needs a plan for credential management.What happens on validation failure?
Your app should fail safely. Decide whether to block, retry, or ask for a different verification path.How do we monitor abuse patterns?
You want a way to distinguish normal traffic spikes from automation attempts.Do we have a fallback path?
If the captcha service is unreachable, your app should have a documented behavior instead of improvising.Does the vendor limit data collection appropriately?
First-party data only is a reassuring posture for teams that want to keep data handling simpler.
That last point matters more than many teams expect. The more a captcha product depends on opaque third-party signals, the harder it can be to reason about privacy, compliance, and user trust.
Choosing the right option for your product
There is no universal “winner” among advanced captcha plugins. reCAPTCHA may be familiar, hCaptcha may fit a different threat model, and Cloudflare Turnstile may be attractive for low-friction web flows. But if your product needs multi-platform SDKs, server validation endpoints, and a straightforward operational model, it’s worth evaluating providers that were built with those constraints in mind.
For teams that want to test a multi-surface integration, CaptchaLa offers a practical starting point, with docs at docs and plan details at pricing. The free tier starts at 1,000 verifications per month, with Pro tiers from 50K to 200K and Business at 1M, so you can validate the fit before committing to a larger rollout.
Where to go next: review the integration guides in the docs or compare plans on pricing to see which setup matches your traffic and platform mix.