If you want to add captcha in WordPress, the safest path is to protect the forms that matter most—login, registration, password reset, comments, and checkout—without turning every visit into a challenge. The goal is simple: block bots where they cause damage, while keeping real users moving.
For most sites, that means choosing between a plugin-based setup and a custom integration. Plugins are quicker; custom integrations give you more control over when and where challenges appear. Either way, the implementation should be server-verified, rate-aware, and tuned to your actual traffic patterns.
What to protect first in WordPress
WordPress is flexible, which is exactly why bots target it so often. A single site can expose multiple entry points: wp-login.php, WooCommerce checkout, contact forms, comment forms, newsletter signups, and custom forms built with plugins. You do not need to guard every field equally. Start with the highest-risk actions.
A practical priority list looks like this:
- Login and registration forms, because credential stuffing and fake account creation are common.
- Password reset flows, because they are often probed for abuse and enumeration.
- Checkout and promo-code forms, because bots can inflate traffic, test cards, or scrape offers.
- Contact and lead forms, because spam can drown out real submissions.
- Comments and public posting endpoints, if your site allows them.
That order matters because captcha should be applied where a challenge is justified. Overusing it on low-risk pages can frustrate users and lower conversions. Underusing it on sensitive endpoints leaves you open to abuse.
If you already run a security plugin, check whether it only adds client-side friction or whether it verifies tokens server-side. A captcha that can be replayed or skipped in the backend is mostly theater.
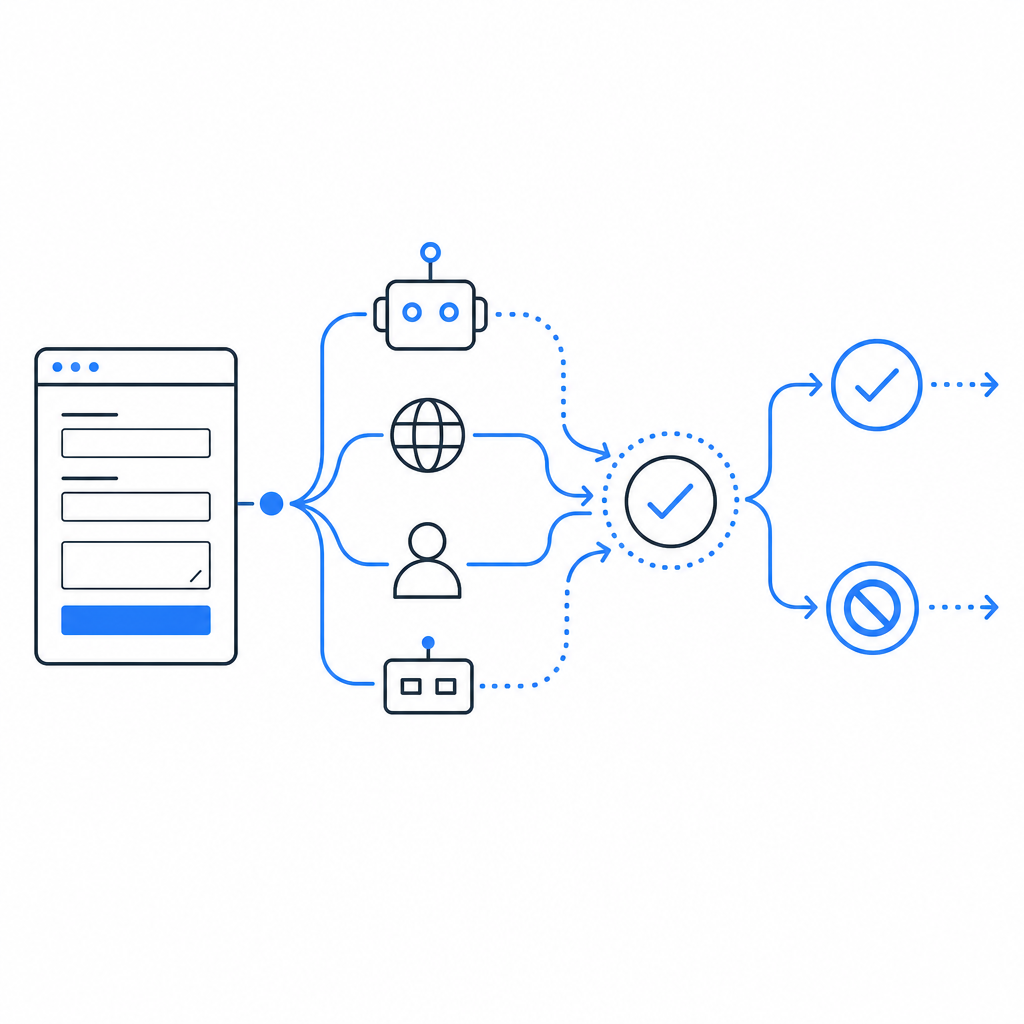
Three ways to add captcha in WordPress
There are a few common integration paths, and the right one depends on how much control you want.
| Approach | Setup effort | Control | Typical fit |
|---|---|---|---|
| Plugin-only | Low | Medium | Standard login/comment/contact forms |
| Plugin + backend validation | Medium | High | WooCommerce, membership sites, custom forms |
| Custom API integration | Higher | Highest | Complex workflows, multi-step forms, headless WordPress |
A plugin-only route is fastest if you just need basic protection on common WordPress forms. A lot of site owners prefer this because it avoids touching application code. The tradeoff is that plugin behavior can be limited when you want custom challenge timing or more advanced risk decisions.
A plugin plus backend validation is usually the sweet spot. The front end can render the challenge, but your server still decides whether the submission is valid. That’s the important part: the browser is never the final authority.
A custom integration is the best fit when WordPress is part of a larger stack. For example, you might have WordPress front-end forms talking to a separate API, or you may want to challenge only after a suspicious action rather than on page load. If you need that level of control, a service like CaptchaLa can be used as a first-party bot-defense layer rather than a generic checkbox.
A secure implementation pattern
No matter which captcha provider you use—reCAPTCHA, hCaptcha, Cloudflare Turnstile, or another service—the backend verification step should be non-negotiable. Here is the basic pattern:
<?php
// English comments only: verify a captcha token server-side before accepting a form submission.
$pass_token = $_POST['pass_token'] ?? '';
$client_ip = $_SERVER['REMOTE_ADDR'] ?? '';
$payload = [
'pass_token' => $pass_token,
'client_ip' => $client_ip,
];
$ch = curl_init('https://apiv1.captcha.la/v1/validate');
curl_setopt($ch, CURLOPT_POST, true);
curl_setopt($ch, CURLOPT_POSTFIELDS, json_encode($payload));
curl_setopt($ch, CURLOPT_HTTPHEADER, [
'Content-Type: application/json',
'X-App-Key: YOUR_APP_KEY',
'X-App-Secret: YOUR_APP_SECRET',
]);
curl_setopt($ch, CURLOPT_RETURNTRANSFER, true);
$response = curl_exec($ch);
curl_close($ch);
// Check the response and accept or reject the request accordingly.A robust validation flow should include these checks:
- Extract the challenge result from the submission, not from a hidden trust flag in the browser.
- Send the token to your verification endpoint over HTTPS.
- Include the client IP when available, since it can help bind the validation to the request context.
- Reject missing, expired, or malformed tokens before processing business logic.
- Log failures separately from successful submissions so you can detect spikes.
If you need to issue server-side challenge tokens, CaptchaLa also exposes a server-token flow via POST https://apiv1.captcha.la/v1/server/challenge/issue. That can be useful when you want the server to decide whether a challenge should even be shown.
For WordPress, the easiest place to wire this in is usually a custom plugin or a small mu-plugin. That gives you access to form hooks and lets you apply captcha selectively. If you are integrating with a form builder, use its submission hooks rather than trying to patch output HTML alone.
How WordPress teams usually configure it
WordPress sites differ a lot, but the deployment pattern is often similar:
- Load the client script from
https://cdn.captcha-cdn.net/captchala-loader.jsonly on pages that need it. - Render the widget or challenge container in the form markup.
- Capture the resulting pass token on submission.
- Verify the token on the server before saving the request, creating a user, or placing an order.
- Add fallback handling for cases where JavaScript is blocked or the challenge cannot load.
CaptchaLa supports 8 UI languages and native SDKs across Web, iOS, Android, Flutter, and Electron, so if your WordPress site is part of a broader product family, you can keep the bot-defense behavior consistent across platforms. It also has server SDKs for captchala-php and captchala-go, which can simplify the backend piece if WordPress is exchanging data with other services.
That matters for agencies and teams running multiple properties. You may have one WordPress install, one mobile app, and one admin panel, but you still want a shared policy for verifying humans and blocking automated abuse.

Choosing between reCAPTCHA, hCaptcha, Turnstile, and a custom provider
There is no universal winner here; the right choice depends on your constraints.
reCAPTCHA is familiar and widely supported, which makes it easy to find tutorials and plugin compatibility. hCaptcha is often chosen when teams want an alternative with a different privacy posture. Cloudflare Turnstile is popular for its low-friction approach and generally lighter user experience.
What you should compare:
- How much user friction the challenge adds
- Whether validation happens server-side
- How easily it plugs into your existing WordPress stack
- Whether you can control challenge timing and placement
- Whether the provider fits your data-handling requirements
If your site handles sensitive forms or multi-step checkout, a first-party setup can be attractive because you can keep the verification flow aligned with your own domain and request lifecycle. CaptchaLa, for example, is designed around first-party data only, which is a useful property when you want tighter control over what leaves your application boundary.
Pricing also matters. A free tier with 1,000 monthly requests can cover small sites and staging environments, while Pro and Business tiers make more sense once your traffic grows into the tens or hundreds of thousands. You can review the current plan details on the pricing page if you are sizing the deployment.
Common mistakes to avoid
A lot of WordPress captcha projects fail for the same reasons:
- They protect only the front end and skip backend validation.
- They add captcha to every page instead of just risky actions.
- They forget to test mobile, accessibility, and JavaScript-off behavior.
- They log too little, making abuse hard to diagnose later.
- They install multiple anti-bot tools that conflict with each other.
A good rule of thumb is to start narrow, measure the effect, then expand only if needed. If comment spam is your main problem, protect comments first. If fake signups are the issue, focus on registration. If credential stuffing is the threat, harden login and add rate limiting alongside captcha.
You should also test how the challenge behaves under multilingual WordPress setups, caching plugins, and CDN layers. A form that works perfectly on localhost can fail when a page is cached, minified, or served through an optimization plugin that strips scripts.
If you want implementation specifics, the docs are the best place to map the client and server steps to your stack.
Where to go next: if you are planning to add captcha in WordPress, review the integration docs first, then pick a plan that matches your request volume on the pricing page.