If you’re seeing “4chan x captcha not working,” the short answer is that the challenge, token exchange, or validation step is failing somewhere between the browser and the verification backend. Most of the time, that means one of four things: the widget didn’t load cleanly, the token expired, the request was blocked or modified, or the site’s verification endpoint rejected the pass token because the secret, IP, or session context didn’t match.
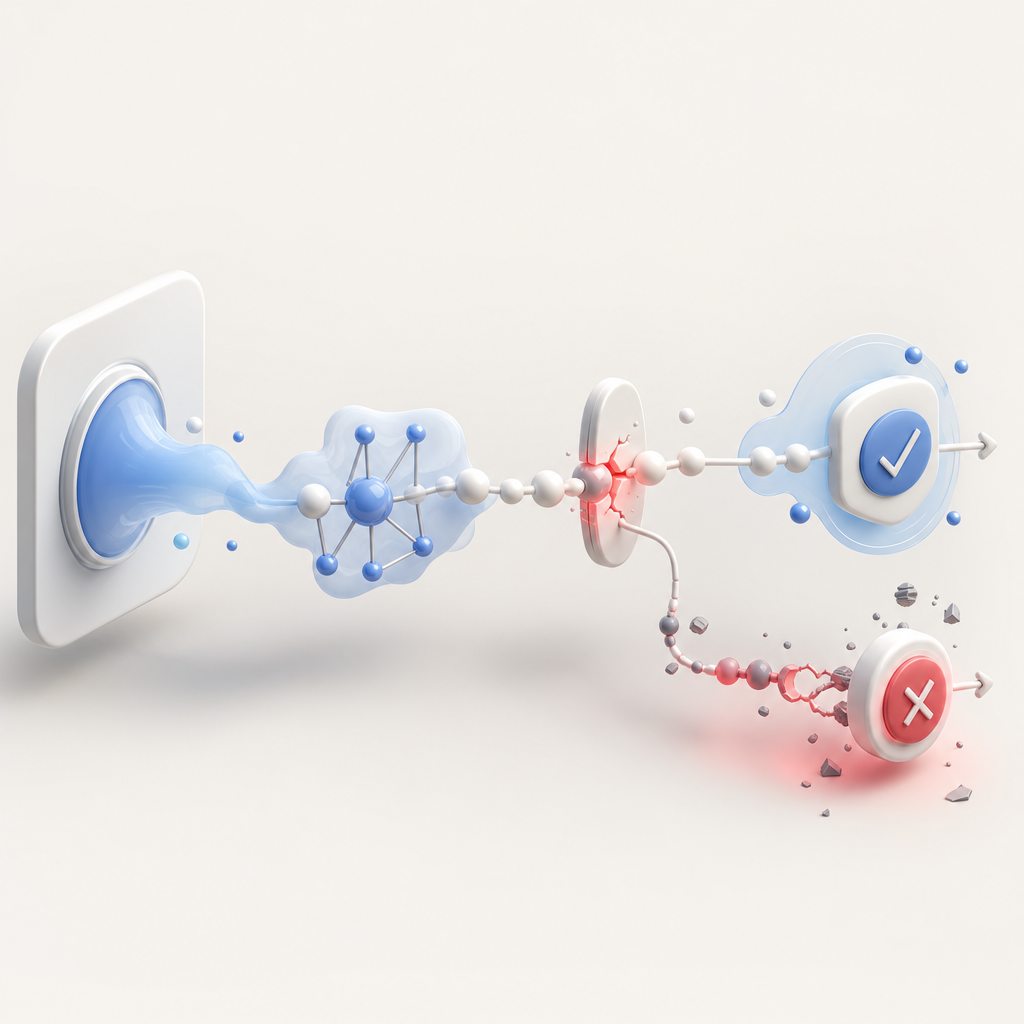
That’s the defender-side version of the problem, and it matters because “captcha not working” is rarely a single bug. It’s usually a chain reaction across frontend delivery, browser state, and server validation. If you’re operating a protected form, login, or post flow, the fix is to inspect the full path rather than just the visual challenge.
What “not working” usually means in practice
When people say a CAPTCHA is not working, they may be describing very different failure modes:
- The challenge never appears.
- The challenge appears, but completion doesn’t produce a pass token.
- A token is generated, but the server rejects it.
- The page refreshes, loops, or times out after the challenge.
- Only some browsers, devices, or regions fail.
For defenders, the important distinction is where the break happens.
Frontend delivery failures
A challenge can fail before any real verification occurs if the loader script is blocked, cached incorrectly, or loaded in the wrong order relative to your app bundle. This is common with strict CSP rules, ad blockers, misconfigured service workers, or race conditions in single-page apps.
If you’re using CaptchaLa, the loader is delivered separately and should be treated like any other third-party script that needs explicit allowlisting and stable initialization. The same general principle applies to reCAPTCHA, hCaptcha, and Cloudflare Turnstile: if the script doesn’t reliably load, the UX fails before validation even begins.
Validation failures
A token can still fail even if the challenge looks successful. Typical causes include:
- Expired pass token
- Token reuse
- Mismatched client IP
- Incorrect
X-App-Key/X-App-Secret - Bad JSON body formatting
- Duplicate submission due to retry logic
Captcha systems are designed to be disposable and short-lived, so treating them like long-term session cookies is a mistake.
The technical path that should work
From a defender perspective, the safest way to debug is to verify the request chain in order:
- Load the challenge script.
- Issue the challenge or render the widget.
- Collect the pass token from the client.
- Send the token to your backend.
- Validate it server-side.
- Allow or deny the protected action.
With CaptchaLa, the server validation endpoint is:
POST https://apiv1.captcha.la/v1/validate
The expected body includes:
{
"pass_token": "string",
"client_ip": "203.0.113.42"
}And the request must include X-App-Key and X-App-Secret.
A separate challenge issuance flow may also be used server-side:
POST https://apiv1.captcha.la/v1/server/challenge/issue
That division is important. The browser should collect proof; the server should verify it. If those responsibilities get mixed together, debugging becomes much harder.
Minimal validation pattern
1. Receive protected form submission
2. Read pass_token from request body
3. Read client IP from trusted proxy headers or connection info
4. POST token + IP to verification endpoint
5. If valid, continue business logic
6. If invalid, reject and log the reasonThe main thing to avoid is trusting the token on the client alone. A successful browser event is not the same as a verified server decision.
Why 4chan-style traffic often exposes edge cases
The phrase “4chan x captcha not working” usually shows up in places with high traffic churn, aggressive refresh behavior, anonymity tools, or users behind shared network infrastructure. Those conditions are tough on any CAPTCHA system because they create noisy signals and unstable client context.
Common stressors include:
- Rapid page reloads that invalidate in-flight tokens
- Shared IPs that make client attribution harder
- Privacy tools that strip cookies or scripts
- Cross-origin embeds that break storage or CSP assumptions
- Mobile browsers that suspend scripts when backgrounded
- Proxy chains that obscure the true client IP
None of these mean the CAPTCHA is broken by default. They mean your implementation has to be resilient.
Compare the usual failure patterns
| Symptom | Likely layer | Defender-side check |
|---|---|---|
| Widget never renders | Script/load layer | CSP, ad blockers, JS errors, network failures |
| Challenge completes but submit fails | Backend validation | Token freshness, secret, payload format, IP match |
| Works on desktop, fails on mobile | Browser/runtime | WebView quirks, background suspension, storage restrictions |
| Works for some regions only | Network/proxy layer | CDN reachability, IP normalization, firewall rules |
| Random loops or duplicates | App state | Double submit, retry logic, stale tokens |
This is why providers like reCAPTCHA, hCaptcha, and Cloudflare Turnstile all emphasize full integration testing, not just visual verification. The visible challenge is only one slice of the system.

How to diagnose the issue without guessing
If you’re maintaining a protected flow, don’t start by changing providers. Start by collecting evidence.
1) Check the browser console and network panel
Look for:
- 4xx or 5xx responses on the loader or validation endpoints
- CSP violations
- Mixed-content errors
- CORS misconfiguration
- JavaScript exceptions during widget initialization
If the page uses a framework with hydration, confirm the CAPTCHA component mounts only on the client side when appropriate.
2) Confirm token freshness
A pass token should be treated as short-lived and single-use. If your app stores it and replays it later, validation may fail.
3) Verify client IP handling
If your backend validates client_ip, make sure you’re extracting the actual client IP from a trusted source. Behind reverse proxies or CDNs, the apparent remote address may not be the real one. Inconsistent IP extraction is a frequent cause of false failures.
4) Audit retry behavior
If the frontend auto-retries a form submission after a timeout, you may be sending the same token twice. The first request passes; the second fails, and the user sees a confusing “captcha not working” message.
5) Test on real networks
Use:
- A normal broadband connection
- Mobile data
- A shared office or VPN connection
- At least one privacy-hardened browser profile
If the issue only appears under one network condition, the problem is probably not the CAPTCHA provider alone.
Choosing an integration that is easier to support
The best CAPTCHA is not just about friction; it’s about predictable integration. If your stack spans web, mobile, desktop, and server-side APIs, the SDK and deployment model matter as much as the challenge itself.
CaptchaLa supports 8 UI languages and native SDKs for Web, iOS, Android, Flutter, and Electron. It also offers server SDKs such as captchala-php and captchala-go, which can reduce glue code in backend services. For package-specific installs, the documented artifacts include Maven la.captcha:captchala:1.0.2, CocoaPods Captchala 1.0.2, and pub.dev captchala 1.3.2.
That said, the same debugging principles apply across providers. Whether you use docs, reCAPTCHA, hCaptcha, or Turnstile, the health of the integration depends on:
- stable script delivery,
- trustworthy token handling,
- correct backend validation,
- and logging that shows where failure happened.
If you need to estimate scale or choose an operating tier, pricing can help you map traffic to plan limits. CaptchaLa’s tiers include a free tier at 1,000 validations per month, Pro for 50K–200K, and Business at 1M. It also follows a first-party-data-only approach, which is worth factoring into compliance reviews.
Practical fix checklist
If “4chan x captcha not working” is your current problem, use this sequence:
- Confirm the loader script is reachable and allowed by CSP.
- Make sure the widget or challenge mounts once, not repeatedly.
- Capture the pass token immediately after successful completion.
- Send the token to your backend without modifying it.
- Validate it server-side with the correct secret.
- Pass a trustworthy client IP when your provider expects it.
- Log the exact rejection reason and token age.
- Re-test on a clean browser profile and a separate network.
If you do those eight things, you’ll usually find the issue quickly.
Where to go next: if you want implementation details or request/response examples, start with the docs. If you’re planning a rollout or comparing volume tiers, check pricing.